16 Cybercrimes covered under Cybercrime Prevention Act – Republic Act 10175
Republic Act 10175 – Cybercrime Prevention Act was signed into law last September 12, 2012. This law is already in effect as the Supreme Court uphold its constitutionality (February 18, 2014). Although some provisions were deemed as unconstitutional (struck down) particularly Sections 4(c)(3), 7, 12, and 19.
It is a law considered to be 11 years in the making as various groups, organizations, and personalities lobbied for its passage. It took awhile for the law to be passed as legislators and various stakeholders need to understand the magnitude of cybercrime and whether the penalty provisions indicated in the E-Commerce Law – Republic Act 8792 is sufficient or not.
At a PTV4 Forum on Anti-Cybercrime Law, Department of Justice Assistant Secretary Geronimo Sy explained that laws on cybercrime are considered as the 3rd building block of legislations necessary to protect the people from crimes committed in cyberspace and use of ICT.
I always look at cybercrime as something under the 2nd block or special penal laws (where I think the E-Commerce Law is in). Although it seems there is now a set of laws in place that are already in that 3rd block and increasing further (which may already include the E-Commerce Law as it is the first policy in place against hacking and online piracy).
As we use and integrate ICT and Internet in our lives, perhaps it is possible that new forms of crimes can happen online and where broader or special legislation will have to be created (that provides mandate for resource allotment too). Nevertheless, that perspective, whether agreeable or not, brings the importance of having more organized groups of netizens who can interact with policy makers proactively on Internet / ICT related policies and do its share of stakeholder consultation.
From my review and understanding, the law:
1. Penalizes (section 8) sixteen types of cybercrime (Section 4). They are:
| Types of Cybercrime | Penalty |
| 1. Illegal access Unauthorized access (without right) to a computer system or application. |
Prision mayor (imprisonment of six years and 1 day up to 12 years) or a fine of at least Two hundred thousand pesos (P200,000) up to a maximum amount commensurate to the damage incurred or BOTH.————————If committed against critical infrastructure:Reclusion temporal (imprisonment for twelve years and one day up to twenty years) or a fine of at least Five hundred thousand pesos (P500,000) up to a maximum amount commensurate to the damage incurred or BOTH |
| 2. Illegal interception Unauthorized interception of any non-public transmission of computer data to, from, or within a computer system. |
– same as above |
| 3. Data Interference Unauthorized alteration, damaging, deletion or deterioration of computer data, electronic document, or electronic data message, and including the introduction or transmission of viruses.Authorized action can also be covered by this provision if the action of the person went beyond agreed scope resulting to damages stated in this provision. |
– same as above |
| 4. System Interference Unauthorized hindering or interference with the functioning of a computer or computer network by inputting, transmitting, damaging, deleting, deteriorating, altering or suppressing computer data or program, electronic document, or electronic data messages, and including the introduction or transmission of viruses.Authorized action can also be covered by this provision if the action of the person went beyond agreed scope resulting to damages stated in this provision. |
– same as above |
| 5. Misuse of devices The unauthorized use, possession, production, sale, procurement, importation, distribution, or otherwise making available, of devices, computer program designed or adapted for the purpose of committing any of the offenses stated in Republic Act 10175.Unauthorized use of computer password, access code, or similar data by which the whole or any part of a computer system is capable of being accessed with intent that it be used for the purpose of committing any of the offenses under Republic Act 10175. |
– same as above except fine should be no more than Five hundred thousand pesos (P500,000). |
| 6. Cyber-squatting Acquisition of domain name over the Internet in bad faith to profit, mislead, destroy reputation, and deprive others from the registering the same. This includes those existing trademark at the time of registration; names of persons other than the registrant; and acquired with intellectual property interests in it.Those who get domain names of prominent brands and individuals which in turn is used to damage their reputation – can be sued under this provision.Note that freedom of expression and infringement on trademarks or names of person are usually treated separately. A party can exercise freedom of expression without necessarily violating the trademarks of a brand or names of persons. |
– same as above |
| 7. Computer-related Forgery Unauthorized input, alteration, or deletion of computer data resulting to inauthentic data with the intent that it be considered or acted upon for legal purposes as if it were authentic, regardless whether or not the data is directly readable and intelligible; orThe act of knowingly using computer data which is the product of computer-related forgery as defined here, for the purpose of perpetuating a fraudulent or dishonest design. |
Prision mayor (imprisonment of six years and 1 day up to 12 years) or a fine of at least Two hundred thousand pesos (P200,000) up to a maximum amount commensurate to the damage incurred or BOTH. |
| 8. Computer-related Fraud Unauthorized input, alteration, or deletion of computer data or program or interference in the functioning of a computer system, causing damage thereby with fraudulent intent. |
– same as aboveProvided, That if no damage has yet been caused, the penalty imposed shall be one (1) degree lower. |
| 9. Computer-related Identity Theft Unauthorized acquisition, use, misuse, transfer, possession, alteration or deletion of identifying information belonging to another, whether natural or juridical. |
– same as above |
| 10. Cybersex Willful engagement, maintenance, control, or operation, directly or indirectly, of any lascivious exhibition of sexual organs or sexual activity, with the aid of a computer system, for favor or consideration.There is a discussion on this matter if it involves “couples” or “people in relationship” who engage in cybersex. For as long it is not done for favor or consideration, I don’t think it will be covered. However, if one party (in a couple or relationship) sues claiming to be forced to do cybersex, then it can be covered. |
Prision mayor (imprisonment of six years and 1 day up to 12 years) or a fine of at least Two hundred thousand pesos (P200,000) but not exceeding One million pesos (P1,000,000) or BOTH. |
| 11. Child Pornography Unlawful or prohibited acts defined and punishable by Republic Act No. 9775 or the Anti-Child Pornography Act of 2009, committed through a computer system. |
Penalty to be imposed shall be one (1) degree higher than that provided for in Republic Act 9775, if committed through a computer system. |
| ****** Unsolicited Commercial Communications (SPAMMING) THIS PROVISION WAS STRUCK DOWN BY THE SUPREME COURT AS UNCONSTITUTIONAL. |
|
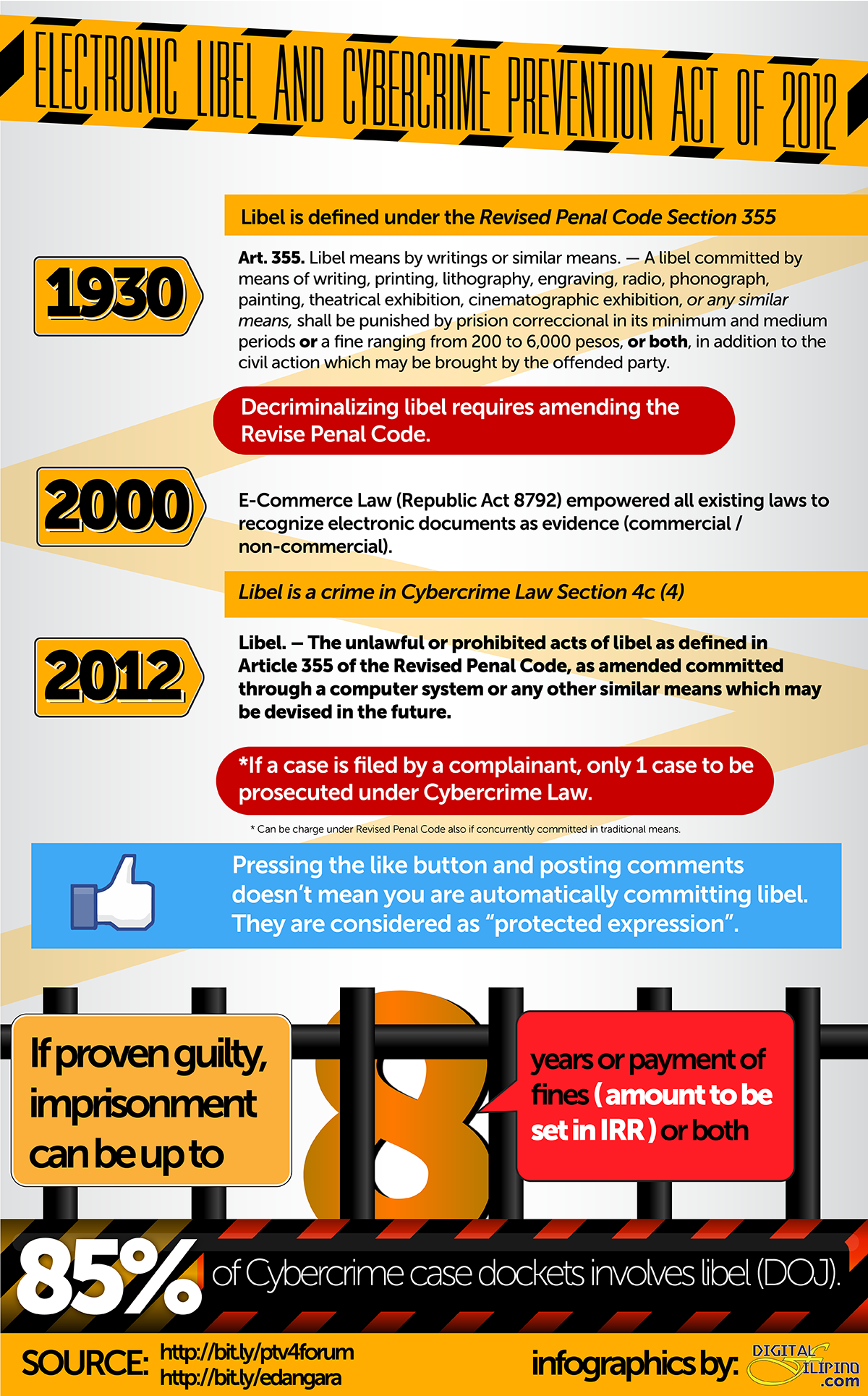
| 12. Libel Unlawful or prohibited acts of libel as defined in Article 355 of the Revised Penal Code, as amended committed through a computer system or any other similar means which may be devised in the future.Revised Penal Code Art. 355 states Libel means by writings or similar means. — A libel committed by means of writing, printing, lithography, engraving, radio, phonograph, painting, theatrical exhibition, cinematographic exhibition, or any similar means, shall be punished by prision correccional in its minimum and medium periods or a fine ranging from 200 to 6,000 pesos, or both, in addition to the civil action which may be brought by the offended party.The Cybercrime Prevention Act strengthened libel in terms of penalty provisions.The electronic counterpart of libel has been recognized since the year 2000 when the E-Commerce Law was passed. The E-Commerce Law empowered all existing laws to recognize its electronic counterpart whether commercial or not in nature. |
Penalty to be imposed shall be one (1) degree higher than that provided for by the Revised Penal Code, as amended, and special laws, as the case may be. |
| 13. Aiding or Abetting in the commission of cybercrime – Any person who willfully abets or aids in the commission of any of the offenses enumerated in this Act shall be held liable. | Imprisonment of one (1) degree lower than that of the prescribed penalty for the offense or a fine of at least One hundred thousand pesos (P100,000) but not exceeding Five hundred thousand pesos (P500,000) or both. |
| 14. Attempt in the commission of cybercrime Any person who willfully attempts to commit any of the offenses enumerated in this Act shall be held liable. | – same as above |
| 15. All crimes defined and penalized by the Revised Penal Code, as amended, and special laws, if committed by, through and with the use of information and communications technologies shall be covered by the relevant provisions of this Act. | Penalty to be imposed shall be one (1) degree higher than that provided for by the Revised Penal Code, as amended, and special laws, as the case may be. |
| Although not exactly a cybercrime, I am including this here as penalties are also imposed by the law. 16. Corporate Liability. (Section 9) When any of the punishable acts herein defined are knowingly committed on behalf of or for the benefit of a juridical person, by a natural person acting either individually or as part of an organ of the juridical person, who has a leading position within, based on:(a) a power of representation of the juridical person provided the act committed falls within the scope of such authority;(b) an authority to take decisions on behalf of the juridical person. Provided, That the act committed falls within the scope of such authority; or(c) an authority to exercise control within the juridical person,It also includes commission of any of the punishable acts made possible due to the lack of supervision or control. |
For sanctioned actions, Juridical person shall be held liable for a fine equivalent to at least double the fines imposable in Section 7 up to a maximum of Ten million pesos (P10,000,000).For neglect such as misuse of computer resources that resulted to cybercrime committed in organization physical or virtual premises or resources, juridical person shall be held liable for a fine equivalent to at least double the fines imposable in Section 7 up to a maximum of Five million pesos (P5,000,000).Criminal liability may still apply to the natural person. |
If you are going to include all provisions in the Revised Penal Code, there can even be more than 16 types of cybercrime as a result.
2. Liability on other laws
Section 7 was struck down by Supreme Court as it violated the provision on double jeopardy.
3. Jurisdiction
(a) The Regional Trial Court designated special cybercrime courts shall have jurisdiction over any violation of the provisions of this Act including any violation committed by a Filipino national regardless of the place of commission. Jurisdiction shall lie if any of the elements was committed within the Philippines or committed with the use of any computer system wholly or partly situation in the country, or when by such commission any damage is caused to a natural or juridical person who, at the time the offense was committed, was in the Philippines. (section 21)
(b) For international and trans-national cybercrime investigation and prosecution, all relevant international instruments on international cooperation in criminal maters, arrangements agreed on the basis of uniform or reciprocal legislation, and domestic laws, to the widest extent possible for the purposes of investigations or proceedings concerning criminal offenses related to computer systems and data, or for the collection of evidence in electronic form of a criminal offense shall be given full force and effect. (section 21)
This gives the Philippines the ability to participate in treaties and of mutual cooperation with countries that have counterpart legislation effectively – especially – on cybercrime cases that have team members or victims residing in the Philippines.
4. Responsibilities of the Philippine National Police (PNP) and National Bureau of Investigation (NBI)
The law gave police authorities the mandate it needs to initiate an investigation to process the various complaints/report it gets from citizens. There are instances of online attacks, done anonymously, where victims approach police authorities for help. They often find themselves lost in getting investigation assistance as police authorities can’t effectively initiate an investigation (only do special request) – as their legal authority to request for logs or data does not exist at all unless a case is already filed. (which in case of anonymously done – will be hard to initiate)
I truly believe in giving citizen victims, regardless of stature, the necessary investigation assistance they deserve. This law – gave our police authorities just that.
The PNP and NBI shall be responsible for the enforcement of this law. This includes:
(a) The PNP and NBI are mandated to organize a cybercrime unit or center manned by special investigators to exclusively handle cases involving violations of this Act. (Section 10).
(b) The PNP and NBI are required to submit timely and regular reports including pre-operation, post-operation, and investigation results and such other documents as may be required to the Department of Justice for review and monitoring. (Section 11)
(c) THE SUPREME COURT STRUCK DOWN SECTION 12 THAT IS SUPPOSED TO authorize law enforcement authorities, without a court warrant, to collect or record by technical or electronic means traffic data in real-time associated with specified communications transmitted by means of a computer system. (Section 12) Getting a COURT WARRANT is a must.
(d) May order a one-time extension of another six (6) months on computer data requested for preservation. Provided, That once computer data preserved, transmitted or stored by a service provider is used as evidence in a case, the mere furnishing to such service provider of the transmittal document to the Office of the Prosecutor shall be deemed a notification to preserve the computer data until the termination of the case. (Section 13)
(e) Carry out search and seizure warrants on computer data. (section 15) Once done, turn-over custody in a sealed manner to courts within 48 hours (section 16) unless an extension for no more than 30 days was given by the courts (section 15).
(f) Upon expiration of time required to preserve data, police authorities shall immediately and completely destroy the computer data subject of a preservation and examination. (section 17)
5. The responsibility of service providers (SP)
Service provider refers any public or private entity that provides to users of its service the ability to communicate by means of a computer system, and processes or stores computer data on behalf of such communication service or users of such service. (Section 3(n).
(a) SP upon receipt of a court warrant from police authorities to disclose or submit subscriber’s information, traffic data or relevant data in its possession or control shall comply within seventy-two (72) hours from receipt of the order in relation to a valid complaint officially docketed and assigned for investigation and the disclosure is necessary and relevant for the purpose of investigation. (section 14)
(b) The integrity of traffic data and subscriber information relating to communication services provided by a service provider shall be preserved for a minimum of six (6) months period from the date of the transaction. Content data shall be similarly preserved for six (6) months from the date of receipt of the order from law enforcement authorities requiring its preservation. (Section 13)
(c) Once computer data preserved, transmitted or stored by a service provider is used as evidence in a case, the mere furnishing to such service provider of the transmittal document to the Office of the Prosecutor shall be deemed a notification to preserve the computer data until the termination of the case. (Section 13)
(d) Upon expiration of time required to preserve data, SP shall immediately and completely destroy the computer data subject of a preservation and examination. (section 17)
(e) Failure to comply with the provisions of Chapter IV specifically the orders from law enforcement authorities shall be punished as a violation of Presidential Decree No. 1829 with imprisonment of prision correccional in its maximum period or a fine of One hundred thousand pesos (P100,000) or both for each and every non-compliance with an order issued by law enforcement authorities.
Service Provider protection insofar as liability is a concern is already covered under the E-Commerce Law.
6. Responsibility of individuals
(a) Individuals upon receipt of a court warrant being required to disclose or submit subscriber’s information, traffic data or relevant data in his possession or control shall comply within seventy-two (72) hours from receipt of the order in relation to a valid complaint officially docketed and assigned for investigation and the disclosure is necessary and relevant for the purpose of investigation.
(b) Failure to comply with the provisions of Chapter IV specifically the orders from law enforcement authorities shall be punished as a violation of Presidential Decree No. 1829 with imprisonment of prision correccional in its maximum period or a fine of One hundred thousand pesos (P100,000) or both for each and every non-compliance with an order issued by law enforcement authorities.
7. Inadmissible evidence
(a) Any evidence procured without a valid warrant or beyond the authority of the same shall be inadmissible for any proceeding before any court or tribunal. (section 18)
8. Access limitation
The Supreme Court struck down Section 19 of the law that gives the Department of Justice powers to order the blocking of access to a site provided there is prima facie evidence supporting it.
9. Cybercrime new authorities
(a) Office of Cybercrime within the DOJ designated as the central authority in all matters relating to international mutual assistance and extradition. (section 23)
(b) Cybercrime Investigation and Coordinating Center (CICC) an inter-agency body to be created under the administrative supervision of the Office of the President, for policy coordination among concerned agencies and for the formulation and enforcement of the national cybersecurity plan. (section 24)
CICC will be headed by the Executive Director of the Information and Communications Technology Office under the Department of Science and Technology as Chairperson with the Director of the NBI as Vice Chairperson; the Chief of the PNP, Head of the DOJ Office of Cybercrime; and one (1) representative from the private sector and academe, as members. (section 25)
The CICC is the cybercrime czar tasked to ensure this law is effectively implemented. (section 26)
Although the law specifically stated a fifty million pesos (P50,000,000) annual budget, the determination as where it would go or allotted to, I assume shall be to the CICC.
DEBATE / DISPUTE on the Cybercrime Prevention Act.
In my discussion with lawyers, journalist, bloggers, among others, concerns were raised on how the law can be in violation of the Constitution and other laws. This includes:
1. Discrimination against online crime.
In crimes committed online, the law gives a higher penalty compared to its offline counterpart. This is seen as a violation of principles within the E-Commerce Law where both offline and online evidence is given equal weight. In its implementing rules and regulations, it also indicated not to give special benefit or penalty to electronic transactions just because it is committed online.
However, I note that perhaps the reason for this also is to increase the penalties. The original Revised Penal Code, for example, gives a penalty for libel in the amount of up to six thousand pesos (P6,000).
2. Did the Cybercrime Law criminalize online libel? Will it result to double jeopardy?
Some see the Cybercrime Law as enabling criminalization of online libel. I think that is not correct.
Libel is a criminal offense as defined under the Revised Penal Code.
The E-Commerce Law empowered all existing laws to recognize its electronic counterpart. It recognized both commercial and non-commercial in form. This made electronic documents (text message, email, web pages, blog post, etc) admissible as evidence in court (and can’t be denied legal admissibility just because it is electronic form and has the same primary evidence weight). Existing penalties under the laws where offense fall in shall apply. That is why the filing of libel cases committed electronically became possible in the past years (and there were cases filed, some won, some lost, and some are ongoing).
Libel is already a criminal offense under the Revised Penal Code as is. Then it got extended to its electronic form since 2000 (with the recognition of its electronic form provided by the E-Commerce Law) with existing penalties applying to it. With the Cybercrime Law, it increased the penalty further if committed with the use of ICT.
According to Atty. Geronimo Sy (Department of Justice), during the PTV4 Forum on Anti-Cybercrime Law, a complaint on electronic libel will only have one (1) case to be filed. The maximum penalty for electronic libel is 8 years.
Hitting the “Like” button on Facebook does not make you commit the act of libel. In this ANC interview, Senator Ed Angara clarified that posting a comment where you get to share your thoughts is covered under “protected expression”.
The amount of penalty is still to be set by the DOJ as there is usually no automatic degree scaling in special penal laws. If a person who got accused of committing electronic libel also did the same in traditional (offline) form, only one case shall be filed. It will be interesting to see how the DOJ will implement the scaling in effect as a result of this.
The mention of libel in the Cybercrime Law is the most contested provision in the law. The additional penalties is seen to curtail freedom of expression. Most of the petitions against the Cybercrime Law focused on this provision.
Numerous legislators are already expressing interest as well in amending the Cybercrime Law and Revised Penal Code.
3. Real-time data access
I appreciate the need for real-time access to data, such as cellular traffic data, especially in tracking scammers and any critical incident as it happens (such as kidnapping and other in-progress crimes) where immediate access is important.
However, the mining of this data for surveillance can be seen as subject abuse. Furthermore, if no intervention such as a judge approval, comes first before getting access where need can be justified.
Although I think this will slow down the process if anything needs court approval first. But other parties believe that this is a must requirement. As the Supreme Court struck down Section 12, I hope processes will be set-up to assist law enforcement with its investigation, to fasten court warrant issuance, especially as it receives complaints from victims of cybercrime.
As the Cybercrime Law gets upheld by the Supreme Court, here are my personal notes on the development of its implementing rules and regulations:
1. Ensure that procedures for police assistance and securing court orders will be fair regardless whether complainants can afford a lawyer or not to assist them.
2. Make the process for data access efficient so that text and online scams culprits can be made accountable soon while ensuring that the data collected won’t be abused.
I am glad that lobbying moves to strike down the whole Cybercrime Prevention Act (Republic Act 10175) did not prosper. The law has greater purposes and intentions that can be helpful in protecting the interest of our netizens and country online.
Will update this document further (to be continued)





Comments (61)
does downloading through utorrent, bit torrent, etc, belongs to the scope of the cybercrime law?even if the contents downloaded were already old?like old movies, songs etc?
Yes it is. But only if the copyright holder will be the one to sue you.
Is the libelous or defamatory exchange in the PM inbox of Facebook can be used as evidence for Libel in RA 10175?
Yes it can be since the year 2000 when the E-Commerce Law or Republic Act 8792 was passed.
Sakop po ba yung panghahack ng facebook account? and paggamit nung account na yun para siraan sa ibang tao?
Papasok na po yun sa identity theft which is also under cybercrime law if gumamit ng electronic means.
pano po pag mga menor de edad ang involve? pinagtutulungan nila sa group chat at may isa member n ginamit pa ang name ng father ng inaaway nila para mang-asar?
i’ve been trying to file a case against my neighbors but they have been continously blocking all evident proof and other forms of evidence, they have tried all sorts of ways just for me to send the given pictures and videos how should i consult the NBI or the PNP with the correct approach on this? since i already tried but authorities here in Dumaguete are still naive about the cybercrime law, and by far has been gradually increasing with more of my friends experiencing the same technical issues i’m dealing with. They are using the OS program Linux, please give me an IT or Programmer who’s under the supervision of the NBI or the PNP to contact in region 7 please.
Hello sakop po b nito yung pag sell online. Niloko po kasi ako ng pinagbilihan ko ng laptop. May sira yunf item. Ano pwede kong icase dun? Thank you.
Hi Dhan. You can file a complaint sa NBI or PNP. Cover siya ng Consumer Act of the Philippines.
Hi po. Ah ma’am i would like to ask if sakop ba nito kapag ba yung naka away mo is post ng post online pero shes not naming you . She has a lot of post po ma’am concerning to our fight. Amd even using bad words. ? Her post dont contain my name and the case po is sinasabi niyang chinismis ko siya about sa pagkakaroon po niya ng ibang kinakasama and nagpapabayad po siya sakin ng 10k for moral damage. I cant afford to pay her so she posted a lot na. Po what case can i file to her?
If it does not mention you in anyway – it will be hard to push it. Unless this person started giving clues that will clearly allude to you.
Good day po. Just want to ask lang po, there’s this someone na post ng post and throwing shades against me using shared post. hindi ko po pinapatulan, until one time, pictures ng anak ko na ang pinost to throw shades, (which I have screenshots) I started to post things condemning the action without naming anyone. And parang gusto pa po akong baliktarin na ako ang namamahiya, Just incase, pasok po ba yun for cyberbulliying/cybercrime law kung magfile sya against me?
Sakop po ba yung. Pag scam? Yung sabi investment daw po. Nag deposit kami sa account nila. Tapos after a week nag down system nila at after ilang days nag Declare sila ng bankruptcy 🙁 paano po kaya kami makakahabol sa pag refund ng pera namin:(?
Ask ko lang po, na scam po kami 6 kami nasa worth 100k.
Nagtatago na yung tao pero tine-trace namin.
Wala po kasulatan pero meron pong text and chat.
Ano po gagawin namin?
Does the libelous or defamatory exchange in the PM inbox of skype can be used as evidence for Libel in RA 10175?
It can be. But it will also put the person sharing that conversation at risk for violating confidentiality.
Hello mam Janette, saklaw po ba ng cyber libel pag tinawag kang malaking satanas sa facebook post
If some body blackmails some one to post their nude pictures online . Does it comes under cyber crime?
Yes and other related crimes (including extortion).
hello..i need some advice 🙁 what are the needed steps to be done by someone who has been victimized by cyber crimes such as phishing, illigal interceptions of gadgets like cp tablet and cctvs leading to a planned deterioration of a person’s identity who has been suffering from mental and financial abused that lasted for more than 3yrs..combined with the used of several people by doing some other forms of mental tortures to aide on this issuesAnd is there any Support Groups for those people who suffered for the same experiences, issues/concerns? thank you so much for your future reply :-). i will highly appreciate it….
does cyber crime include remarks made on viber chat group( viber chat group composed of 12 members). remarks were accusations & character assasinations like how u dress up/ how u dance etc. after 2 hrs bashings the one who formed d viber group chat evicted me
Sakop din po ba nito yung binuksan ang fb account mo, binasa ang mga PMs mo, at nag print out pa po?
Hi Good Day,
If your daughter/ son received a tweet from another student and was verified that the tweet came from one student stating “ pakielamero kaputa ka! ….. My classmate ……… is a bitch….
Ano po ba ang pedeng gawin as a parents? Sakop po va ito ng cyber bullying?
Maraming sa,amat po.
Nathaniel
Is hacking online games account covered dito? Pero wala pong money nainvolve pero para game may value po siya? Tanong ko lang po sana kasi may game policy din kasing nakalagay na trade at your own risk thank you po
Hi! Good Day! Does this law include the unauthorized access of Facebook account, reading all the private message of Facebook conversation.I have experienced that my former boss used to access my Facebook account, read the messages, screenshot some of the conversation,provide a print out and used against other people without my computer consent.
Hi ma’am,sir:
Ask ko lang po kung pwede po bang kasuhan ang hipag ko na masyadong nampapahiya sa anak ko sa lahat po ng post nia?nakalagay din po sa lahat ng post nia ang name ng anak ko…ano po ba ang dapat kong gawin?masyado na pong napahiya ang anak ko sa mga post nia sa facebook…thank you in advance po for your reply.
Sakop po ba nito ang pagpost nila na patay na ang anak mo and claiming na anak niya ang shinare nyang photo?
If you have transactions via web apps and eventually ask for a refund but they keep on telling that they’re working on it. Its been 2months of waiting and yet i havent received any refunds, does that fall on this category?
Kasama ba sa cyber libel kapag minura ka sa isang viber group chat? As in minura ka ng PI na nabasa ng lahat ng members who are all prominent people..?
I recently got an email regarding a blackmailing me for apparently getting into an x-rated website. Stating that i should send him money in order to cover up for the damages he might apparently do. Saan ko kaya siya pwede isumbong? Mukhang US based ang taong ito, or if not baka dito lang.
And, I have not even made a visit to any x rated site, ever.
Hello po! Sakop po ba ang illegal na pag open ng facebook account at pangingialam ng messenger ng ibang tao?
May classmate po kasi ako na nakialam ng fb account ng isa ko pa pong classmate, nagbasa po siya at nagbackread ng conversations namin sa group chat. 6 lang po kaming member ng group chat na yon pero ung classmate ko pong nagbasa hindi po siya kasali don. Ngayon po, nagscreenshot po siya nung mga pinag-usapan namin and kinalat po niya sa buong klase namin, nakaabot pa po sa mga prof. Tanong ko lang po kung sakop po ba ng cybercrime law ung ginawa niya and pwede po ba siyang kasuhan about don? Salamat po
Ano pong pwdeng isampang kaso sa dati kong kalaguyo na patuloy na nag sesend me messages sa asawa ko para tuluyan kaming maghiwalay. Gusto na po naming mag move forwars at ayusin ang family namin pero itong taong ito ayaw tumigil sa pagsira saakin para hiwalayan ako ng mr ko.
My girlfriend and stay in a know hotel in manila, one night my girl friend went out of our room and i was not there,since i am the registered guest,my girlfriend was subjected to security procedure wherein she was asked to undress in a small room for security check,to her surprise she later seen a cctv camera installed on that room, does the hotel commit violation on her privacy.
Hi po…
is sending of message by unknown profile on facebook
forcing someone to do something is a crime?
Sakop po ba ito yung nagpost ng nude pic ng bata para ipakita ang mga sugat sugat at kung anong kalagayan ng bata?
Nahulihan ko ang mister ko ng ibat ibang fb acct at puro teenagers ang mga chinachat nya at tinatanong nya kung gustong makapanood ng sex video. May pumapayag kaya napapadalhan nya.
Isa sa mga kachat nya nagsbi sya (mister ko) na padalhan siya ng nakahubad at nagpadala nga ng napakaraming pictures nya na nakahubad. Sa kasunod na kachat ng mister ko pinadala nya ang mga ito sa kakilala nung babae.
Ano ang pwede kong gawing hakbang (ikaso) sa knya dhil una, matagal na niya akong winawalang hiya. 2nd gusto ko ng matigil na o kundi man ay mabigyan siya ng kaso?
How does it wprk when the accused is not within the philippines?
Paano nila na po-proved ang illegal access to a computer or application? For example someone logged in my computer. Ginamit ang social media account ko para maka panira ng ibang tao. How can they proved kung sino ang gumamit sa PC illegally?
Hello po good afternoon..ask ko lang po Kung pwede ko kasuhan Yung tao Kasi nag post po siya pinangalanan Niya ako at sinasabi na linoko ko daw which is Hindi Naman po totoo..
Hello po. Someone sent a private message sa friend nya tagging me and my partner as “mga magnanakaw” with our photo below the message and even said that i stole the money of a specific call center campaign sa center na dati kong minamanage. Her friend sent me the screenshot of that message. Matibay po ba yung evidence ng libel? And ano pa po ang cases na pwedeng ifile against her?
If some body blackmails some one to send their intimate videos to other people. Does it comes under cyber crime? and where should we file a case and what are the penalties for this? Thank you!
Pano po ung akin mam nag order ako online sa kapit bahay ng kapatid ko binayadan ko na lahat afternoon almost 2 months ng di pinapadala item nung finofollow up ko blinock ako pag tatawagan ko kinakancel ang call so ang ginawa ko since my isa pa akong account ung convo namin na ng aask ko why 1 month ng bayad ung item wala pa at ung patunay na nakablock ko nilagay ko sa comment box ng isa sa mga pictures nya. Kasi i tried messaging here sa inbox gamit ung isang account ko you cannot send message to this person ang lumalabas considered cybercrime po ba ung ginawa ko?
Hi po i need help.
sakop ba ng online libel ung pananakot or black mail na ilalabas ung sex video kapag nagkahantungan sa kasuhan
kc po balak ko po magpannull sa asawa ko tapos ginagamit nya ung sex video n nangyari before n nagkapirmahan kami sa amicable settlement.
ngaun marami xang minimessage through messnger n kamag anak or family ng GF ko. na sinisiraan nya ung GF ko tapos ilalabas ung sex video namin.
pwede ba xang makasuhan ng e libel tapos extortion
or anu magandang gawin
salamat po sa response nu
Is it possible to file a cyber libel case on a anonymous deleted facebook account? What are needed to do so.
Pwede po ba kasuhan yung isang tao or ang company na anti-cybercrime law dahil piang-tittext nila yung mga frined at client ko na may utang ako sa kanila.
Nakuha nila yung mga contact number sa phonebook ko kaya sila nakapag-text sa mga friend at clinet ko,Parang gusto nila akong ipahiya at minsan tinawagan pa nila ang isa sa cellphone number na tinext nila at sinisigawan pa.
Someone uses my photo for a dummy account in a purpose of online shaming. He/she shared one of my post tapos i-aadd nya po mga fb friends ko. Sa comment section nya po ako sinisiraan. Ano po ba dapat kung gawin?
posting of cheating/illicit affairs conversation sa instagram. does it comes under cyber crime?
pwede po bang makasuhan dito sa Pilipinas ang taong nagtthreat thru online kahit nasa ibang bansa siya at ang taong tinethreat niya ay nandito sa Pilipinas? Kung hindi po pwede sa Pilipinas, saan po pwede magfile ng kaso at anong kaso pwede ifile sa kanya?
Hi! Have a good day po. Meron po akong common law wife at meron na po kaming mga anak. Dpa kami kinakasal for some reason. Magkasama po kami dati sa iisang lugar, means iisang laptop ang gamit namin sa bahay ang di nya po alam eh nasave nya ung FB password nya laptop na gamit namin. Then last April 2017, diko alam if ano nag-udyok sa akin para buksan ko ung FB nya the isang gabi I discovered something na kachat nya sa FB Messenger with green chat, ung chat na di para sa dmo karelasyon then ung usapan po nila green is umabot sa nagVideo chat sila for maybe 15 minutes. Dahil di kami magkasama ng common law wife that time, nagchat ako sa kanya then pinapaamin ko ko cya if sino ung katawagan nya that night kahit alam ko na po kasi nakita ko na po ung chat nila. Until umamin cya nag video call nga pop sila then umabot nagJak*l or nagsarili na daw po ung lalaki at sabi ng comonlaw wife eh wala nmn daw cyang ginawa or pinakita sa lalaki. Pinatwad ko po at nagTRUST ako sa kanya na dna nya uulitin yun.
Now po just this April 2019, parang may nagtulak na nmn sa akin na iOpen ung FB account same FB sa 2017 same password. Meron po ulit nadiscover na kachat nya sa FB messenger ulit, Then ganoon po ung ulit ung usapan this time again parang ung common law ko ang nagbibigay ng motibo for the green chat po ulit then kinausap ko po cya then naging OK na po kami, sabi nya na wala lang daw po un. At dahil sa di po ako mapakali dahil alam ko na meron something sa kanila BASE po sa takbo ng usapan nila sa chat. Nagduda po ako na gagawa ulit ung commonlaw wifeko ng isang FB account just to chat this GUY at sa inaasahan pagkakataon po binisita ko po FB profile nung Guy then by checking the guy’s FB friends I discovered something in guy friends list, meron isa cyang friend kakaiba sa lahat ng friend nya kasi bukod sa IBA UN NAME na nakalagay, meron din syang 2 friends, ung at ung main FB ng common law wife ko. Then I smelled something wrong, then that point my laptop mouse pointer sa friend ng guy na kakaiba ung name un po nakita ko ung name at middlename ng common law wife ko, ung po ginawang username sa FB like www, facebook. com/namengcomonlawwifeko. Coincidence po cguro kasi nagtry po akong open ung second FB account ng common law wife ko at naalogin ko nga po kasi parehoa lang sila ng password sa main FB account nya. Un nga po meron clang chat at ganoon parin pon pattern ng chat nila meron parin mga green chat like,:
Girl: Saglit lang ligo lang ako
Guy: Tara sabay tayo
Girl: Taran halika dito
Guy: magvideo ka nlng para exciting
Girl: Ayoko
Guy: ay boring, Cge na papanoorin kita
…
Guy: miss ko na yang bibingka mo. Papakin ko yan bukas. Mabango ba yan?
Girl: Adto diri lagi (punta ka nlng kasi dito) dko alam if tama ung translate ko
Marami po silang usapan na ganyan. At kaninang nilogin ung secong FB ng commoc law wife ko is nakikita kong nilologin din dya kasi naglogin logout cya ng 2 beses. So means gamit nya itong FB na ito just to chat the GUY.
Now po, I have all the screenshot of their conversations with the first guy and the second guy. Including my conversation with common law wife ko pinaamin ko po sa ginawan nilang nung first GUY.
Balak ko na po kasing isumbong sa TATAY nyang Pastor and of course po showing all the evidence I have para po maniwal po sila. Natatakot po ako kasi baka PWEDE akong kasuhan ng Cyber Cdahil nilogin ko FB account ng commonlaw wife without her permission na iLogin ko po at ipapakita ko kasi ung mga conversation nila as my evidence na meron cyang ginagaw na di maganda. If meron po akong kaso, kaya ko po bang ipanalo, if di kayang ipanalo, base po sa salaysay ko po mga ilang years ang kulong ko or ilang libo ang maging danyos ko po?
Sana po mapayuhan nyo po ako. Salamat po ng marami.
Have you ever thought about publishing an e-book or guest authoring on other sites?
I have a blog based on the same topics you discuss and would really like to have you
share some stories/information. I know my visitors
would appreciate your work. If you are even remotely interested, feel
free to shoot me an e mail.
[…] https://digitalfilipino.com/introduction-cybercrime-prevention-act-republic-act-10175/ […]
[…] Toral, J. (2019, Feb. 10). 16 Cybercrimes covered under Cybercrime Prevention Act – Republic Act 10175. Retrieved from https://digitalfilipino.com/introduction-cybercrime-prevention-act-republic-act-10175/ […]
[…] read more : https://digitalfilipino.com/introduction-cybercrime-prevention-act-republic-act-10175/ […]
hi po. wala po b pwede ikaso sa mga scammer online? 3x n po ksi ako nscam last dec.2020 and until now ng scam p din yung mga scammer sa facebook. madami n po kasi sila naloko even ofw from around the world. sana po matulungan nyo po ako
[…] 16 Cybercrimes covered under Cybercrime Prevention Act – Republic Act 10175 […]
[…] Toral (2019) Click here to read more about Janette Toral’s review and understanding of the Law Click here to read more about The Republic Act […]
[…] 16 Cybercrimes covered under Cybercrime Prevention Act – Republic Act 10175 […]
pwde po masakasuhan yung friend ko na pinagsasabihan niya ako nang nagpakanton at sinabihan niya din family ko na magsasaka kc po visay po ako at sinabihan niya po ako ng visayang palaka paa niya lang po daw ako ang may mga mura din siya sabi sa akin lahat po nang chat niya sa akin sa messenger sana po matulungan niyo ako ano pwde case sa kanya sana po help po ako or advise about jan
[…] Analysis of the Cybercrime Prevention Act […]